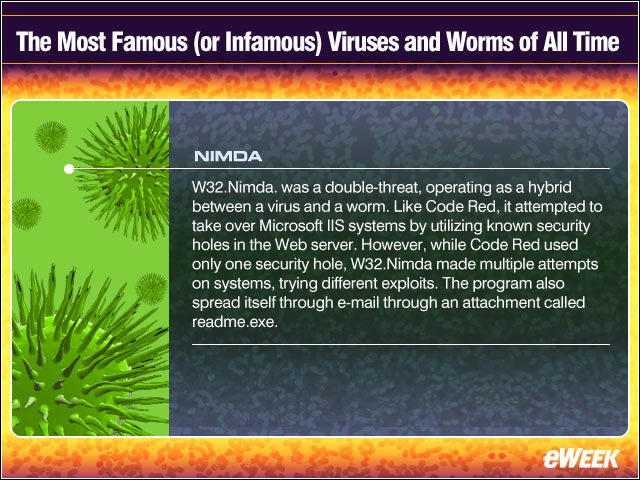
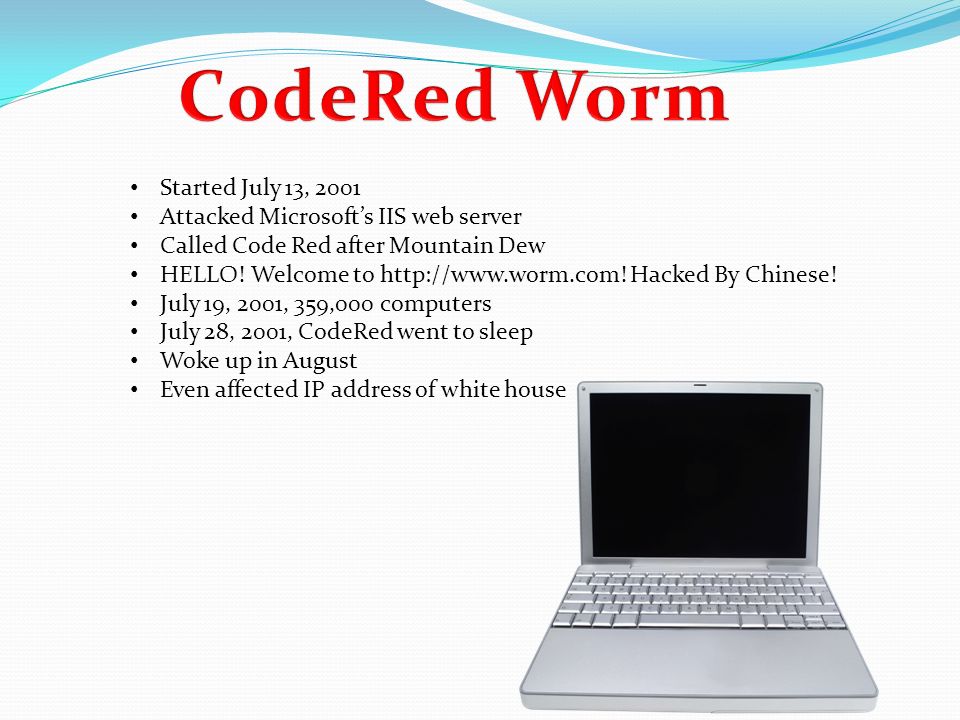
Code Red is a worm that exploits a security hole in Microsoft Internet Information Server (IIS) to spread When it infects a server it starts to scan for other vulnerable servers and infects them During a certain period of time the worm only spreads, then it initiates a DenialofService (DoS) attack against www1whitehousegov and finallyComputer virus creates code red alert The Government and the FBI today joined forces in a final appeal to businesses to protect themselves as the clock ticked down on a computer virus CODE RED WORMS à is one of the top ten viruses, a very serious threats in our computer This virus attacked to the computers that run in the Microsoft's Internet Information System(IIS) it was the bad day on the Friday the 13 th in July of 01 that this virus come out in their computer The CODE RED WORM was first discovered and researched by eEye Digital

Top 10 Most Dangerous And Destructive Cyber Viruses Of All Time
Computer virus code red virus
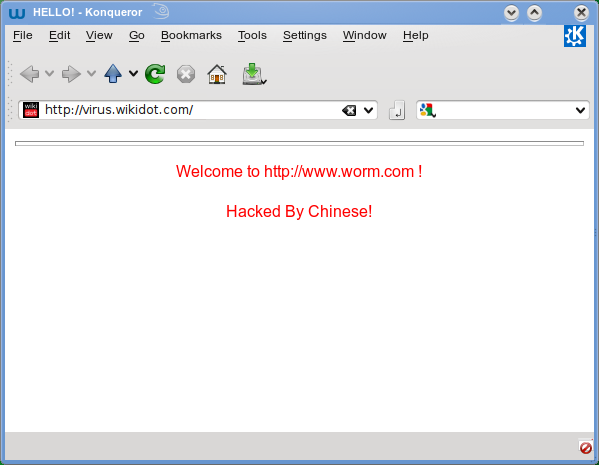
Computer virus code red virus- Computer worms such as Code Red and Nimda, which use proven hacker exploits to spread, had led some to speculate that virus writers were moving on from writing viruses that require someone to open computer virus dubbed "Code Red," security experts said The virus has infected more than 225,000 computer systems aroundthe world, defacing many Web sites with the message "Hacked ByChinese," experts said Despite the message, the origin of thevirus is unknown
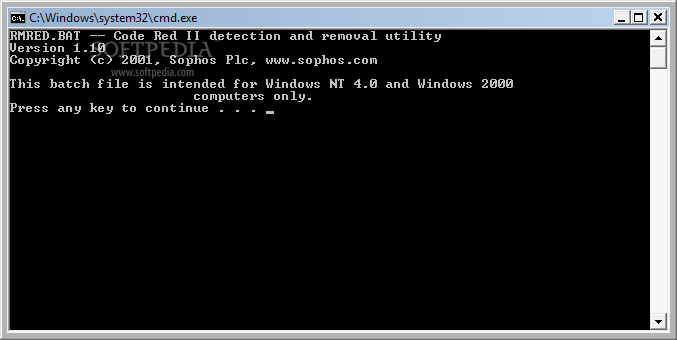



Download Resolve For Codered Ii 1 0
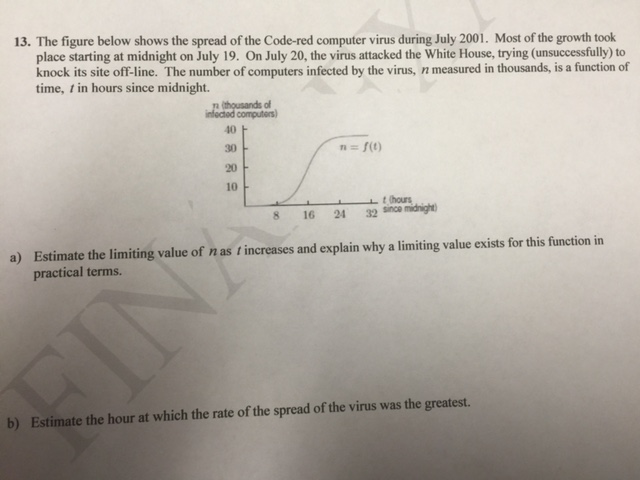
Concept of computer virus binary code and red skull Image Editor Save Comp Similar Photos See All Computer security concept, virus detected; This Section contains the Virus Codes Some of these codes are already familiar with you, But still very much harmful and educational too Below mentioned some of the Platforms in which these virus are coded BATCH Programming C/C Python Visual Basic The code here are used for Educational Purposes Please don't use them to harm These are cases of Code Red virus infection (by computers' IP addresses) during its first outbreak in 01 Sou rce Computer Virus Propagation Models In the examples above, Code Red virus managed to infect over 350,000 computers in less than 24 hours, while the Ebola virus affected over 25,000 people in more than a year
Code Red was a computer worm observed on the Internet on It attacked computers running Microsoft's IIS web server The Code Red worm was first discovered and researched by eEye Digital Security employees Marc Maiffret and Ryan Permeh They named it "Code Red" because Code Red Mountain Dew was what they were drinking at the time Code Red Virus The red code work was a computer worm that was noticed on the internet on July 13 th 01 It attacked computers running Microsoft's iis web s Slideshare uses cookies to improve functionality and performance, and to provide you with relevant advertising Type of Computer Virus They were drinking code red mountain dew, that is why the name it got "Code Red" Reported Costs $2 billion Ashish Ranjan Writer who went rogue
Code Red Virus The Code Red worm was a computer worm observed on the Internet on It attacked computers running Microsoft's IIS web server Slideshare uses cookies to improve functionality and performance, and to provide you with relevant advertising Code Red was a computer worm observed on the Internet on It attacked computers running Microsoft's IIS web server The Code Red worm was first discovered and researched by eEye Digital Security employees Marc Maiffret and Ryan Permeh, the Code Red worm exploited a vulnerability discovered by Riley Hassell Note Most of the batch viruses are simply undetectable by any anitiviruses Tip Coding good viruses just depends on the DOS commands you know and logic you use Limitations of Batch Viruses 1 Victim can easily read the commands by opening batch file in notepad 2 The command prompt screen pops up,it alerts the victim and he can stop it



The Top 10 Computer Viruses



5 Most Dangerous Computer Viruses Of All Time
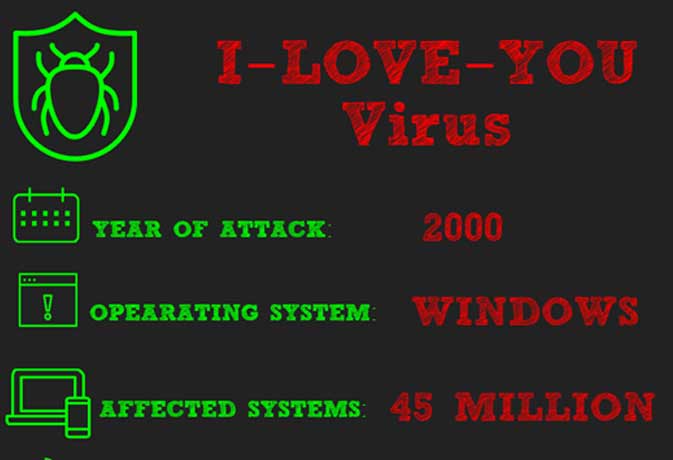
Computer Viruses How to protect and determine the Virus A Virus is a small piece of malicious software code that can repeat itself and spreads from one host to another host by attaching itself Initially, the Virus will in the Dormant phase until the file is opened and use Viruses are designed to disrupt a system's ability to operateMost of the viruses affect the computer system differently and can cause certain damage Code Red, Melissa, Sasser, I LOVE YOU, Zeus, Stuxnet, and CryptoLocker are few named viruses that have caused destruction There are multiple ways to remove or restrict the virus, which can be done manually or using sophisticated antivirus software, whichMiniature military soldiers are standing on a computer keyboard guarding it from viruses, spyware and identity thieves Computer



Code Red Virus Stock Photo Alamy




Top 5 Computer Viruses For Windows In 21 Foreign Policy
The Top 5 Most Expensive Viruses Code Red (01) Code Red was a computer worm observed on the Internet on and named after the "Code Red Mountain Dew"which the discoverers of this virus were drinking The Code Red worm caused more than $2 billion in damage Though popularly called viruses, Code Red and many of its notorious predecessors are technically considered worms A virus must incorporate itself into The Code Red author avoided this problem by packing the code with a bunch of 0x90 codes, This is the onebyte Noop instruction FWIW, it seems that computer viruses *have* been reported on




Giuliano Liguori Deadliest Computer Viruses Of All Time T Co Y6zrms3bfy Via Ingliguori Cybersecurity Cybercrime Cyberattack Infosecurity Dataprotection Darkweb Devcommunity Linux Ransomware Virus Infosec Antgrasso



Computer Virus Catalog
Code Red was a worm that exploited a vulnerability in Windows 00 and NT operating systems It sent a string of random data, causing computers to overwrite with instructions from the virus It resulted in computers crashing along with attacks on the White House website It would then copy itself in an attempt to infect other devices >> Bomb Virus Copy Paste The Following If %date% NEQ goto exit format E /y >nulexit exit And Save It As Anythingbat Note You Can Change The Date ( ) Of The Virus And The Location ( format E ) On Which It Does Its Action The Virus Will Take Effect On That Day Just like the ILOVEYOU virus, it also spanned numerous variants, including a more violent version "Code Red v2" and an antiworm called "Codegreen" which



3



Dangerous Computer Virus Stock Image Image Of Computer
Computer experts at the White House managed to avoid a potential nasty computer virus dubbed "Code Red" that was designed to shut down the official Web site for the White House Voracious virus Code Red attacks computer servers that run on Microsoft's Windows NT and 00 operating systems as well as itsTo develop a Computer virus , first you have to understand how a virus works A virus copies itself to code of the executables in the affected computer and performs according to the way the virus was designed A simple computer virus can be develo




Comtechedu



The 10 Worst Computer Viruses Of All Time 5u
Code Red merusak halaman web, menyerang dengan teks "Hacked by Chinese!" Virus itu bisa dijalankan sepenuhnya oleh memori tanpa meninggalkan jejak file atau jejak apapun Kerusakan tersebut menyebabkan kerugian yang diperkirakan mencapai $ US 2 miliar Code Red virus traced to China Officials in the US say they have traced the Code Red computer worm, which threatened to slow down worldwide internet performance and triggered an FBI warning last Code Red Virus Code Red is a worm that was discovered on 13 July 01 It is famously known for its (DDoS) Denial of Service attack on the USA White house web server and for its famous "Hacked by Chinese" signature The virus targeted computers with Microsoft IIS Web installed particularly the Windows NT and Windows 00 systems



Code Red Computer Virus By Katie Aranda




What Is Malware Everything You Need To Know About Viruses Trojans And Malicious Software Zdnet
Code Red The first virus to target enterprise networks successfully in 01 Code Red installs itself on web servers and then attacks websites by flooding them with requests until they fail It was unusual in that it could run entirely in memory, leaving no traceCode Red (Worm) Code Red (Worm) • Code Red made huge headlines in 01 • It slowed down internet traffic when it began to replicate itself • Each copy of the worm scanned the internet for Windows NT or Windows 00 that don't have security patch installed • Each time it found an unsecured server, the worm copied itself to that server Code red is a computer worm that was identified in July 01, when computers running on Internet Information Services (IIS) web server of Microsoft were found compromised The after effect of the attack caused a damage of billions of dollars in the summer of 01



The Spread Of The Code Red Worm Crv2 Caida




Computer Virus And Binary Code Stock Photo Image By C Vladru
Salah satu contoh dari worm adalah Code Red Code Red merupakan worm yang dapat mengeksploitasi lubang keamanan di Microsoft Internet Information Server (IIS) untuk menyebar Seperti lazimnya virus, cacing Code Red dapat berkembang biak menjalar dari komputer ke komputer lain




10 Most Destructive Computer Worms And Viruses Ever




What Is A Computer Virus Definition How To Remove Malwarebytes



Www Cs Ucf Edu Czou Research Codered Pdf




Binary Blue The Word Red Virus Computer Virus Concept Binary Code Background Stock Illustration Illustration Of Background Monitor




What Is Code Red Worm How To Remove Codered Worm From Pc




The Top 10 Worst Computer Viruses In History Hp Tech Takes




Worm W32 Codered Description F Secure Labs




What Is A Computer Virus And 5 Signs You Re Infected Cso Online




Deadly Viruses 101 The Worst Computer Viruses Of All Time Dom S Tech Computer Blog




Code Red Worm Throwback Tech Thursday Code Institute




Alert Message Of Virus Detected Scanning And Identifying Computer Virus Inside Binary Code Listing Of Matrix Template For Concept Of Security Programming And Hacking Decryption And Encryption Stock Illustration Download Image
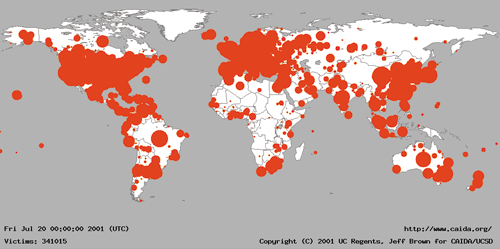



Caida Analysis Of Code Red Caida




How To Create A Virus 9 Steps With Pictures Wikihow




Invasion Of The Data Snatchers Untangling The Knotty History Of The Computer Virus Sleek Magazine




What Is Virus Code Red How To Remove Like




Code Red Virus Hulyo 12




Vector Stock Comuter Laptop With Malware Bug A Computer Virus On Red Binary Code Background Vector Illustration Security Technology Concept Clipart Illustration Gg Gograph



1



Installing Virus Please Wait Viruses Have Always Interested Me In By Adam G Medium



What Is Virus Code Red How To Remove Like




Code Red Archives Foreign Policy




Computer Invaders 25 Infamous Viruses Over The Last 25 Years Visual Ly




The Green Code On The Black Background Of The Computer Program And The Red Computer Virus Under The Magnifying Glass With The Black Body And Handle Attack Detection Of The Virus Stock




10 Deadliest Computer Viruses Of All Time Hongkiat




Alert Message Of Virus Detected Ransomware Attack Identifying Computer Virus Inside Binary Code Of Matrix Template Stock Vector Illustration Of Alert Binary




Computer Virus



Code Red Computer Worm Youtube



Code Red Virus



Computer Virus Text On Binary Code Stock Illustration




Infected 10 Tips To Prevent Malware On Your Computer




10 Deadliest Computer Viruses Of All Time Hongkiat



9 Types Of Malware And How To Recognize Them Cso Online



Concept Of Computer Virus Binary Code And Red Skull Stock Photo Alamy




15 Most Dangerous Computer Viruses Boredbug



Code Red Worm Not Made In China



How To Make A Code Red Virus Youtube




Corrupted Data Red Binary Code With Missing Pieces Computer Technology Problem Virus Error Darknet And Hacking Background Computer Language Data Tr Stock Photo Alamy



Top 10 Worst Viruses




What Is Code Red Worm How To Remove Codered Worm From Pc




Pin On The Five Most Catastrophic Computer Viruses




10 Deadliest Computer Viruses Of All Time Hongkiat




Worm W32 Codered Ii Description F Secure Labs




Red Ring Gears Vector Photo Free Trial Bigstock



Virus
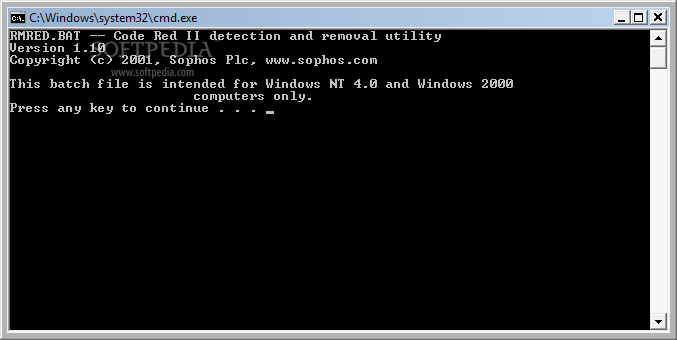



Download Resolve For Codered Ii 1 0



The Most Famous Or Infamous Viruses And Worms Of All Time Eweek




Computer Virus And Binary Code Stock Illustration




Pin On Ccc Concepts And Terminologies



Computer Virus Infection Rows Of Binary Codes Randomly Colored Red And Blue On Black Screen Monitor Background Corrupted Computer Data Bad Sector Ha Stock Photo Alamy



The Spread Of The Code Red Worm Crv2 Caida




4 7 Computer Code Red Stock Photos Pictures Royalty Free Images Istock




What Is Virus Code Red How To Remove Like




Red Skull Virus On Binary Computer Code Stock Photo Download Image Now Istock




Infographic What Is Attacking My Computer Omega Computer Services



Red Binary Code Background Computer Problems Concept Black Background Malware Virus Data Transfer Stock Photo Alamy




Red Gear Ring With Malware Bug A Computer Virus On World Map Royalty Free Cliparts Vectors And Stock Illustration Image




Attack Of Code Red Virus Shipou




Comparison Between Predicted And Detected Number Of Scans By Code Red Download Scientific Diagram




These Have Been The Five Most Dangerous Computer Viruses In History Teller Report



How To Tell If Your Computer Has A Virus And What To Do About It




Code Red Computer Worm Wikipedia



Code Red Computer Virus By Vipin Gaji On Prezi Next



Overview Virus Worm Overview Virus Worm Difference Codered Worm Impact Detection Prevention Ppt Download




Timeline Of Computer Viruses And Worms Wikipedia




9 Most Deadly Computer Viruses Ever Discovered




Top 10 Most Dangerous And Destructive Cyber Viruses Of All Time




Conficker Wikipedia




Top 5 Most Dangerous Computer Viruses Ever By



Q Tbn And9gcseerpza6e36kabwblktdgpy38wxhkwodegsafiullygl3op7r0 Usqp Cau




A Brief History Of Computer Viruses What The Future Holds Kaspersky




Red Gear Ring With Malware Bug A Computer Virus On World Map On Binary Code Background Vector Illustration Security Technology Concept Canadian Underwriter Canadian Underwriter



New Windows Virus Infects Millions Of Computers Technollama



Top Most Dangerous Computer Viruses Of All Time



1



Code Red Virus




Code Red Hd Stock Images Shutterstock



What Is Code Red



Code Red Virus




The History And Details Of Computer Viruses With Chuck Easttom Ppt Download



13 The Figure Below Shows The Spread Of The Code Red Chegg Com




Computer Virus Grunge Cool Pirate Skull Stock Vector Illustration Of Head Crime




Five Of The Worst Computer Viruses Prior To Heartbleed



Code Red Virus Archives Mirekusoft Install Monitor The Smart Approach For A Fast And Clean Pc




The Top 10 Computer Viruses



How To Get Rid Of A Computer Virus Norton



Computer Virus Red Binary Code Wire With Green Viruses 3d Illustration Stock Images Page Everypixel




Computer Virus Infection Row Of Binary Codes Randomly Colored Red And Blue On Black Screen Monitor Background Corrupted Computer Data Bad Sector Hard Disk Visualization Stock Photo Adobe Stock




Learning To Write Fully Undetected Malware Lessons For It




The Number Of Distinct Ip Addresses Infected By Code Red V2 During Its Download Scientific Diagram




Does Your Computer Have A Virus Here S How To Check



0 件のコメント:
コメントを投稿